IT companies selling cyber security services are mostly fakers when it comes to knowing the topic and to make matters worse flat out hypocrites. Wow…bold statement! How do you know? Because we’ve seen it.
The motivator and straw that broke the camels back (and we’ve got a strong back) is this company in Grand Rapids, MI called “Fusion IT”. A colleague of mine from that market texted me their website the other day and said:
“Oh you’ll love this…”
(how did he know LOL)
…”I heard a commercial on this radio voiced by the founder of Fusion IT. He said blah blah blah blah blah blah about cyber security. Then he ended with “God bless””.
Then I said…”Oh gawd”, “Let’s hack them” LOL. I really said that! After some industry banter back and forth my colleague said it was on a radio station called Wood Radio on 106.9 FM. I don’t listen to Wood but I think it’s a newsy right leaning talk radio station so more talk doesn’t drive anyone to change the channel. I’m sure listeners learn about cyber security by osmoses as they tune out the commercials. It’s hard telling how many people’s ears perked up or were even interested in what he was saying BUT hacker talk is in the news, even on stations I listen to like NPR (that doesn’t mean I’m liberal all you conservatives). Hacker talk and cyber security is everywhere online, it affects your daily life by exposing your private information, it now plays a role (allegedly or real) in politics from voting machines to social media trolling BUT not only is all this hacker talk in the news daily; the fear mongers who sell solutions are busy faking it until they’re making it.
Take our competition Fusion IT for example. I checked them out at the promoted URL from the radio spot. They give you good cyber security fear monger stats to gin up your fear so they can sell you the cure:
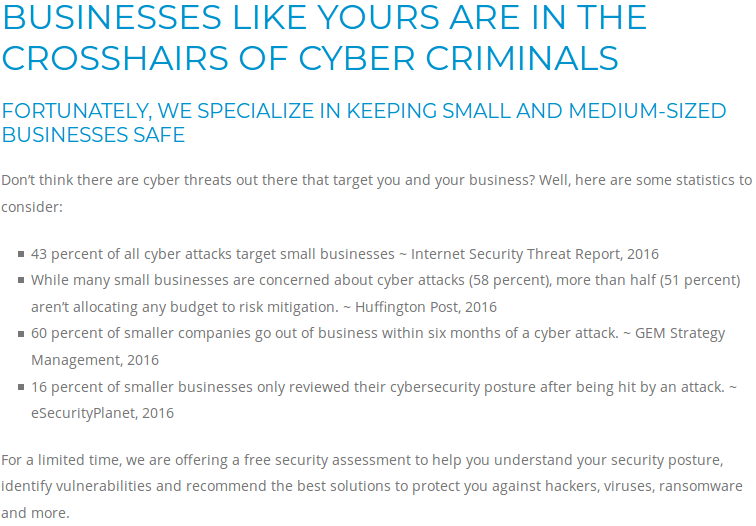
Lets break down what we’re reading:
Fusion’s claims that you’re in the cross hairs ISN’T TRUE! Why? Reading is fundamental and so is comprehension. What do cross-hairs imply? As it relates to hacking, a hacker first cast a wide net to look for general vulnerabilities using wide ranging scanning mechanisms like port scanning looking for services on various ports. Services like email “listen” on any number of ports like port 25 for SMTP or Simple Mail Transfer Protocol or databases “listening” on port 3306, a SQL port that you can connect to database servers on. It’s like a dentist checking for cavities. They don’t just look at one tooth, they look at all your teeth and poke around to find that one weak point where their poker sinks in meaning…you have a soft spot. Do they hit a nerve? Not yet but maybe and if they keep poking…they might find something to drill! Hackers, crackers, jackers, scammers, spammers, phishers, etc all cast wide nets and work from the general to the specific. They look for the easy target. They might target a business in the “cross-hairs” BUT if they target a specific business for starters (which isn’t the norm) there is usually a massive pay off. It’s usually a big firm, hacktivism or someone is paying them to do it like an industry competitor or they have some insider information to get the data. So no, this is Pinocchio growing nose mis-truth…as a general rule for most business the first statement is false. “Crosshairs” implies sniper like intent and quite frankly that’s not how it’s done from a certain perspective.
Fortunately Fusion IT specializes in keeping small and medium sized businesses safe…hmmmmmmm. Really? Why…where did you get this specialized skill set? How prey-tell doth thou keep us safe oh knight of the round cyber table? Mmmmmmm…they don’t go into it as you see at the end you need to contact them for your “free security assessment to help you understand your security posture”…it sounds like you need a security orthotic! The fact is as we’ll see…they and many others including big companies are overpaid derpy know nothing middle-men selling snake oil.
Just the facts:
Lets start with the first quote from a threat report in 2016 which is actually a commentary about 2015 and yes…I’m posting this and their radio advert was in 2018 so…it could be argued it’s a bit dated and they’re not on the bleeding edge of information about the topic. The cited report is put out by Symantec…who makes security products like Norton, spam filtering, malware software and other junkware that doesn’t matter. In my view they’re not a reputable source, they’re a legacy company who gets by on their size like many a bad company (like Micro$oft and Ci$co for example) but lets assume for a moment they are a reputable source.
The quote from the report in context is about email phishing and written horribly but the full quote is:
“In the last five years, we have observed a steady increase
in attacks targeting businesses with less than 250
employees, with 43 percent of all attacks targeted at small
businesses in 2015, proving that companies of all sizes are
at risk.”
Again, this is about phishing, a specific kind of attack and the ugly sister to spamming. There are many types of attacks. Also…you know what’s odd about that statistic? Yes…I’ve put it in bold for you. Symantec considers “small business” companies with less than 250 employees (OK, sure…whatever). How many businesses are in the United States do you think (assuming this is about US based businesses only because I don’t know…I have IT work to do here people I can’t vet everything for you LOL)? I found a PDF from a business database website claiming that in 2013 there were 18,204,679 total business with 67,701 of them having MORE than 250 employees. If we can assume for a moment that these numbers are mostly accurate (and it’s probably close in 2018 or at least the same percentages)…if you do that math that leaves you with a total number of businesses with less than 250 employees at 18,194,978 businesses. That means, the percentage of businesses with less than 250 employees is 99.94% of all businesses. Does that put the 43% of “all attacks” targeting small businesses in 2015 into perspective? Remember…these are specific attacks related to phishing and on top of that it’s a cousin of spam…not a terribly cross-hair like activity. Spear phishing…now that’s targeted with specifics and probably more effective!
That 43% isn’t even half (LULZ) the actual number of small businesses. Is it a large number? Yes BUT as a percentage of the total it’s not and put into the proper context it’s not. In fact, if you think about it…I suspect that 80% of the attacks were caught by spam filters AND that only 20% of the phishing spam got through. So it’s 43% of a subset of an attack that’s likely 80% + filtered that isn’t terribly scary now is it? Maybe you saw 1 in your inbox this week…?
Does it now make sense as to why the next cited statistic makes sense about 58% of businesses don’t give a rip about cyber security? Duh…if you understood the first statistic like we’ve laid it out it’s because they’re not really under attack or I should say…not feeling it. I suspect most businesses have some sort of firewall, spam filter and anti-virus or anti-malware on their desktops already.
Fake News (to use a parlance)!!!
Moving on…what does the Huffington Post know about cyber security anyway? They care about impressions, clicks, click bait, eyeballs and making money off of ginned up reports about all kinds of things including sports and pop culture trash. Citing the Huffington Post further diminishes the credibility of anything Fusion IT is explaining because they neither understand statistics nor do they understand what’s credible. Symatec isn’t credible in my mind who’s got a conflict of interest because they sell the cure to what ails you, nor is the Huffington Post. These aren’t credible sources for knowledge with respect to cyber security in my view. Does Symantec have good information about threats, sure but if they’re trying to sell me something you better believe I question it like nobody’s business and properly vet it. I don’t use Symantec for much of anything and I can’t buy a solution from someone with a conflict of interest like Symantec. They’re everywhere (as we’ll see).
This is going to get long, I can see it already but it’s necessary we go through things tit for tat, bit by bit, derp by derp.
The next statistic is one that should scare you! 60% of smaller companies go out of business within 6 months of a cyber attack. Again, Fusion IT expounds more ignorance on the subject matter (and they’re not the only guilty party which is our point). Boogety boogety BOO! This was actually an article in the Denver Post on October 23rd of 2016 written by Gary Miller who doesn’t know much about cyber security in fact. He’s an “M&A business consultant”…that’s from his LinkedIn page although he’s got an impressive resume and I’m sure he knows what he’s talking about he simply cites another place called “The U.S. National Cyber Security Alliance” (NCSA). M&A is “mergers and acquisitions” not Mcyber & Asecurity (LOL). Gary should go merge…and acquire not cyber & secure. Poor Gary probably doesn’t know that his comments have been leveraged to scare people 😛
You can see here how it’s someone saying something that someone said, that someone said…that someone said who said something that I can use to scare you…BOO! Here’s the quote from the real source:
“The U.S. National Cyber Security Alliance found that 60 percent of small companies are unable to sustain their businesses over six months after a cyber attack. According to the Ponemon Institute, the average price for small businesses to clean up after their businesses have been hacked stands at $690,000; and, for middle market companies, it’s over $1 million.”
I don’t even know how to properly lay this out for reading but…here goes nothing…
Firstly, the NCSA has some real derps sitting on their board and when I say real derps that’s an understatement! LifeLock (part of the Equifax hack), Symantec (where have we heard that name from before?), ADP…the payroll processor who’s been hacked, Wells Fargo…how reputable is Wells these days (more LULZ), they’re contemporary fraudsters and technically…hackers, bilking their customers with mortgage and insurance fraud. I could go on…but I don’t particularly like beating dead horses. NCSA is in my view not reputable. They don’t even define what “small companies” are anywhere that I can find. They’re interested in putting out a fake narrative paid for by companies interested in selling you what they’re selling…cyber security solutions. Moreover…who is this “Ponemon Institute”?
Their website about section is here. What you find is another someone who said organization and an organization that’s in bed with “cyber security” companies to scare and drum up business for themselves and those “in the community”. Another thing I can’t stand is people saying “the community” when they really mean “echo chamber”. Ponemon’s latest report is “sponsored by Palo Alto Networks”. Palo Alto is an overpriced vendor of products who are more hype than anything. Hands down I think they have the best marketing department of any startup networking company ever. Perhaps I’ll blog about that straw man someday. Back to Ponemon. Ponemon offers “strategic consulting”…again, more consulting gigs. I wonder how they get the consulting gigs? I think it’s coming up with scary statistics, scary reports, false naratives and biased data so we can sell people the cure to what ails them! Seems like a consistent theme here. It’s the marketing stupid! Don’t believe the hype! <– Grand Master Flash is the follow up after that song! (hawt)
I wonder why a small business cleanup costs businesses on “average” $690,000 dollars and for middle market companies…over $1 million dollars? It’s the consultants dummy! It’s the Ci$co’s and Micro$ofts of the world dummy! Because they can charge you that much! Why do you think they go out of business? Because they can’t pay that bill! What puts them out of business isn’t the attack it’s the cost of remediation like ANY DISASTER! You know…I’d bet you’d find similar statistics about hurricanes, floods and earthquakes (although I haven’t looked). A cyber attack CAN BE a disaster that’s why you hear about “disaster recovery” solutions like backup plans, etc. You just need to frame this with a different perspective. The companies that got whacked by a malware breach could have costs into the millions because of regulatory fines like HIPAA fines, SEC fines, FINRA fines…who knows, what a mess. They can also suffer losses because they don’t have backups. Backups are the cheapest form of “insurance”, take that to the bank. They can suffer a loss in reputation further diminishing confidence in their brand and thus affects their revenue although this didn’t seem to affect places like Target, Hobby Lobby and Arbys who had major breaches of credit card information on their systems (there are many more that come to mind also like Home Depot). I’d argue the liability of a cyber attack calculates that cost so it’s not only the cost of remediation but it might be. I didn’t scrutinize the study because…as we’ll see, the study methods are spurious.
So…here’s the “Ponemon Study”…I have lots to say about their “methodology” also: Link
Problems:
- Only 126 companies were given the survey and of that 126, 45 did the survey (small sample) and I didn’t even look into what types of companies those were…perhaps they were all fortune 500? That’s not 99.94% of businesses in the US! It’s not even a decent sample size.
- It’s old from 2009 and the study actually BEGAN in 2005. At the time of this post…that’s decade old data.
- What casts doubt on the numbers is this line in the study: “The least expensive total cost of data breach for a company included in our study was $750,000” If the least expensive total cost was $750k…then how is it the average cited by everyone is “$690,000” dollars? Either I’m looking at the wrong study OR someone doesn’t know their own data or it’s someone who mis-said something that someone mis-said, that someone mis-said and as a result is misleading.
- Percentages for the reason companies had this cyber expense were, “system glitch”, “negligence” and only 24% was a malicious attack. Guess what people…hire competence and it’ll CYA 76% of the time (LULZ).
- Page 34 of the Ponemon report is the best reading, I can’t even quote it all without infringing on copy right (LOL). Snippets like: “Non-Statistical Sample” yet everyone is quoting it like gospel. “Sampling-Frame Bias – Because our sampling frame is judgmental, the quality of results is influenced by the degree to which the frame is representative of the population of companies being studied”. I can’t even make this stuff up…we’re biased because we cherry picked out sample data and that sample data was derpy.
Remember…why are we even here? Why am I even talking about this measly straw that broke my back by Fusion IT? I’m the camel remember…because of the fake it till you make it crowd in IT including Ponemon the source of many of the myths about IT security. The “experts” don’t even understand what they’re saying anymore, they take money from “IT security companies” like Palo Alto and have complete hacks spewing out bad data to scare people into more consulting gigs although…at least they’re professional about it (unlike me some might say but I speak the truth and I give money back to “the community” I don’t take it). They have scammers, absolute losers on their boards and advisory councils because those are the companies that have the money (Wells, ADP, LifeLock, Symantec, etc). It’s a rigged game of who can scare you the most, who looks the best, who has the best reputation…marketing, marketing marketing. Don’t believe the hype!
Fusion IT said that Gem Strategy said that Ponemon said…and Gem Strategy didn’t even read the report OR report accurate information about the report and Ponemon’s data is biased and isn’t a statistical sample (their words not mine). My English teacher would crucify me for all the “and’s” in that run on sentence 🙂
All the afore mentioned and the statistics they use are NOT CREDIBLE! I hope you can see this and I hope you can see how big companies selling consulting services and IT security products can’t be trusted if they’re selling with made up statistics from biased and made up studies. Are there threats? You bet BUT how valuable of a target are you and how valuable is your data? You need a sensible approach to your IT security and you probably don’t need 90% of the junk these snake oil peddlers are selling.
Hey everybody…the emperor has no clothes!
Back to Fusion IT (and companies like it). If they knew anything about cyber security they’d know your privacy was important. Guess what they have on their website? Scripts that try and figure out who you are so they can contact you.
Look at the scripts they run on their website:
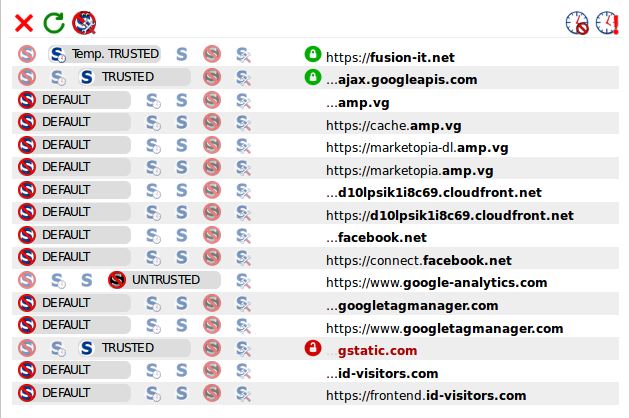
Notice the data thieves who want to steal your privacy:
Google Analytics (full disclosure I also use Big Brother Google on my site)
id-advisors.com <– the most egregiousness violation
id-advisors.com is a data collector from a site called Visual Visitor. On their site they say:
“Designed specifically for Sales people, Visual Visitor provides the following information:
- Who your website visitors are
- What company they are from
- What products or services they are interested in
- Their contact information
- The length of time spent on your site”
What company they’re from? Their contact information? WOW! Great data. Don’t go to Fusion IT’s site if you value your privacy. Of course…I blocked that script so they don’t know I was there…so sneaky. Did I need a VPN or Tor Darkweb browser…nah, simple script blocking blocks their spying ways.
The point is…Fusion IT is already violating your cyber privacy in a major way, it’s not anonymized like Google Analytics where they give you an advertising ID. It’s who you are, what company you’re from and if they have it…your contact information!
Lastly…Fusion IT clearly doesn’t know about cyber security because their web form to contact them doesn’t have bot protection. A clear sign they’re a few Security+ classes short of a useless certification.
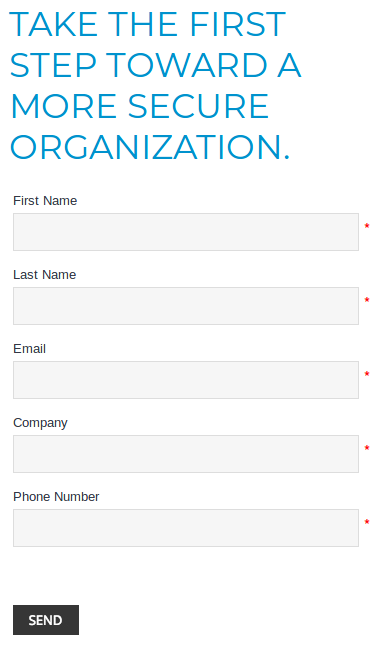
What you can do here is “reverse spam” using their form to put in fake names like “buy viagra” with email accounts you want to spam and company names like “buy cialis” then click send. A confirmation likely goes out to that email thanking them and might have a copy of this information. I don’t really know if it can be leveraged for reverse spam BUT it’s possible and at the very least is a standard web form security practice to put in bot protection, we use them!
In the end don’t believe the hype! Don’t believe the IT hypocrites! Don’t believe the Micro$ofts of the world, the Ci$co’s, the Norton$, the M&A con$ultants and the cyber $ecurity hype. Think about it critically, do your research and when in doubt…ask us what we think.
If you need competence, analytical minds, critical thinkers, researchers, skeptics, out of the box thinking, real IT solutions, expertise, handsome and dashing, terribly humble and funny IT consultants don’t look to Fusion, look to EITS! I’m also available to give dynamic talks about these types of IT topics and more.
800-864-9497
[si-contact-form form=’1′]

One Response