If you’ve read our blogs, heard our talks at our local KLUG group, personally talked to me or conversed via email you all know how much I love Cisco (eye rolls). I was at an event in Lansing, MI recently about small business in Michigan (SBAM). A rather derpy VAR who is quite slick with advertising and marketing had a big graphic about IT Security and Cisco Talos in their booth. You saw it right when you walked into the hall, it was a primo spot and I’m sure the owners cushy board position in the group had no small part in getting placed there! They also hosted a “cyber security” round table, sponsored the event and I’m sure to most they looked HIGHLY CREDIBLE! Promoting Cisco in my view actually discredits you in large part. Here are just a few reasons why:
- Cisco is a legacy company, switching, routing, etc are all commodities and there are perhaps THOUSANDS of companies that can easily do all that, probably quicker, cheaper and better than Cisco in 99% of environments.
- Promoting another company’s solutions makes you look like just a middle man implementor. You’re a line cook not a chef. All you know how to do is work off of a recipe card (as we’ll see). You don’t know how it’s made or what ingredients are needed to change the mix and make something different by adding less of one ingredient and more of another. In fact, quite often they put something in and hope for the best!
- Trusting a vendor solution without proper understanding of what it is you’re leaning on might backfire and often does. You need to know how something works!
- You’re a one trick pony. The only solution you’ll offer is whatever you can make the most money off of or the product that seems to give you the most creditability. You’re not a true solutions company…Cisco is the true solutions company not you.
…I won’t drone on, I think you get the point.
I’m here to say that by in large that presenter and their company are not credible. Why? We’ve not only dealt with their infrastructure before but we’ve stolen it! Indeed…we stole it right from underneath their noses when we migrated their customer off their overpriced cloud infrastructure (LULZ). Really? How did you do this? OMG!
They had a client (their old client) on their “cloud” which by the way…wasn’t a “cloud” at all it was a host in a hosted environment (3 to be exact, a Windows Domain Controller, a Windows file server and a Microsoft Exchange Server) . That company calling it a “cloud” shows me they don’t even know the difference between cloud and hosting! The company was less than friendly about just hading over the keys as you might imagine. They created us a powerless user account and dragged their feet for more than a month. Meanwhile they kept charging the client. They charged a fee for a project manager that did absolutely NOTHING and was a total boat anchor. It’s shameful. I can say this because when the tables were turned and we gave up a client to them guess what we did? That’s right…here you go, here is everything you need, passwords, users, full documentation, etc. If that ever happens again you bet we won’t comply. Thanks but no thanks jerks. So much for professional courtesy! I can’t particularly stand the way these charlatans do business in my region. It is what it is. So this well respected IT company (chuckles) who has expertise in cyber security had one of the end users as a “domain administrator” which allowed me to use that account to then elevate our useless account to something more useful like an “enterprise administrator” thus giving us the power to do anything we wanted INCLUDING accessing, modify and migrate their Exchange server lock stock and barrel! We also had full access to replicate their Active Directory, all their files, policies, user accounts, computer accounts, etc. All we did on the go live date was pull the plug :). It was the most seamless transition our new client ever felt. They didn’t even know anything happened! We made that other company sneaker net a hard drive over in a car just because. We didn’t even need the data because we sync’d it down to our clients local infrastructure. To this day I don’t think they even know how easy it was to seize control of their environment :). This shows me they’re not a true cyber security company. We don’t allocate a domain admin to anyone or an Enterprise admin to anyone BUT the client has full access to their documentation and therefore the God or Goddess mode passwords they need. We don’t use documentation as a form of ransomeware like other IT companies we’ve run into including the one who’s the topic of discussion.
So…these charlatans had a booth and plastered all over they’re talking about IT Security, they hosetd a cyber security round table and they’re promoting Cisco Talos (surprised they didn’t say something about “block chain” while they were at it!). The same group who during the meal time when you listen to the speakers on the main stage left their both with all their laptops unattended! Ha! If that was in a bigger venue they might have come back to the booth with their equipment gone! I was chuckling inside. Absolutely not credible as a cyber security company leaving your equipment unattended! Additionally the FBI representative in the round table was not giving out credible information. Not everything they said but boy some of it was questionable like a virus causing some of the most expensive damage in the history of viruses…the one he mentioned isn’t even a top 10 historically and I didn’t even adjust it for inflation! Furthermore, the FBI is involved AFTER you’re hacked not before so with respect to defense they aren’t great…they just aren’t! Take the FBI’s latest advise on the “VPN filter malware” infecting home grade routers. What’s their solution? Reboot the router! That’s a big LOL! Reboot…so it’ll just come back up and get reinfected. Genius advice FBI. I digress…I could write another blog about the round table discussion and some of the misinformation given out in that meeting with respect to cyber security and some of the things said like…it’s not a matter of if you’ll get hacked but when <– not true!
So here’s how marketing for cyber security works both from the VAR we are discussing and for Cisco. Mind you, the VAR always looks up to Cisco because the VAR isn’t a solutions provider (they’re a cook not a chef) and uses Cisco’s credibility as their own. The VAR was promoting Cisco “Talos” – Talos is a big copper Greek machine meant to “protect” a place called Europa in Crete. As you know…it’s MARKETING! Even in ancient times! It doesn’t actually protect anything now does it?! Granted…they thought it did as part of their belief system I get it but it’s funny to think about it from a marketing standpoint too. The irony is that Cisco Talos doesn’t protect you by in large either in our modern day!
What really? How can you say that Cisco Talos doesn’t protect you? Well…have you ever questioned it? Have you ever asked what does Cisco Talos do for me anyway? Do you just believe like the people of Crete that Talos is circling the island thwarting pirates and invaders all day? Well…for example:
1 – On this page they talk about “Malware Repution”: https://www.talosintelligence.com/reputation_center/malware_rep
That reputation mentioned is actually a bad thing not a good thing. It’s not like they’re the good kind of popular when you make this list.
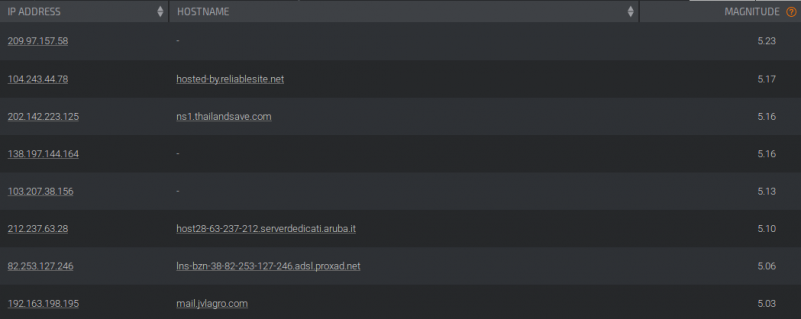
The irony is this…Talos also has an IP black list and the IP’s on this page above, their latest malware reputation list…ARNE’T ON IT!
Their “Talos Intelligence” is actually quite dumb! Isn’t it?
Here’s the link to that list: Talos IP Blacklist
Don’t you think it would be useful to have malware hot zones on the IP black list? Don’t you think it would be helpful for the top spammers to make the list especially considering their payload? In fact…none of those IP’s are on the list! The IP Black List is only at the time of blogging this 1556 IP addresses…not very many at all. It’s tragic actually…and detrimental to your organization if you trust in Talos. If that’s the only thing you’re doing to thwart attacks good luck. Call me when you get a crypto or ransomeware! Our block lists are far more comprehensive and so is our security stack. Talos might as well have port forwards to your server databases! Yikes!
2 – Do you think the VAR’s selling Talos actually vet what Cisco is doing or promoting or understand how it works? Do you think for one second the VAR who has a vested interest in perpetuating the Cisco lore would speak about Cisco as having any chink in their armor? That wouldn’t be wise now would it? That is…if all you’re interested in is your reseller opportunities and commissions! No way would a VAR do anything to tear down Cisco’s reputation because they leverage it to prop up their own reputation. It reminds me of scam artists really, the old trick where a performer will do a trick which really isn’t that great but they have “marks” in the audience to gin up the crowd or the mark gets picked to come up on stage to give the magician assistance but the crowd doesn’t know that mark is actually part of the act and on the payroll. It’s essentially a massive conflict of interest. Cisco does a great job at propagating this too with training classes, certifications to no end, complicated infrastructure articles, blah blah blah blah blah. It ends up being an industry in and of itself! Training! All the big tech firms do it so it’s not something Cisco invented, you can probably thank Microsoft for it if I were to guess.
So the answer is no…no the VAR doesn’t vet or question Cisco because Cisco is like a God to them whom also passes down a blessing of assumed credibility to their flock. If they did vet Cisco or knew how to properly vet Cisco they’d realize it wasn’t that good and that what Cisco does is a commodity. I’m not certain they would do something different knowing that in fact because of the conflict of interest, revenue stream it provides and credibility it gives them. VARs would continue on the same track and blame any security breach on something else like “dumb end users” clicking links they shouldn’t have clicked. That actually came up in the meeting in not so clear words because I don’t think anyone called anyone “dumb”…users clicking links they shouldn’t was brought up though. Why would you not block a top malware sender and put them on your black list so the malware or link never makes it to the end user? It makes absolutely ZERO sense Cisco! It makes absolutely ZERO sense VAR! Round table…it makes absolutely ZERO sense! As a side the clicking links mention was in reference to “phishing” and “spear phishing” not general web surfing. There was more misinformation about phishing in that meeting but that’s a discussion topic for another blog post. I’m sure their spam filter is yet another Cisco or reseller system they know very little about or they’re relying on their support team to maintain it. It’s highly likely they don’t having experience with them.
So summarize…
Cisco is a legacy company, so are VARs and so are their solutions. Cisco Talos does very little for you or your organization although I bet you’re paying for it! Additionally guess who gets called in to cleanup a mess? The FBI, Cisco & Microsoft which mostly bankrupts companies because of their fees for service. No wonder 60% of business that suffer from a cyber attack go out of business within 6 months. It wasn’t the cyber attack that put you out of business silly it was the fee’s you had to pay for fixing it to Ci$co and Micro$oft! We’ve blogged about this in another post about IT Hypocrites (don’t believe the hype).
Why are we better? OK…so Cisco Talos is dumb now what genius? I need protection! Well you’re in luck. Why? Because we don’t use Cisco Talos! We use an Open Source product that we’ve customized and honed on the edge (our firewall) that faces the Internet…the mote around your organization that controls the draw bridge. You can’t just have a firewall though! That’s just one piece of the stack. We also implement a security stack that we compare to a bullet proof vest. The stack consists of different layers of security policies pushed down to the end user or their devices. If you believe the end users is your last line of defense (and they are) you might be surprised that the end users in our managed environments don’t typically need to think about it because they’re locked down and protected from running software they shouldn’t be running, executing scripts, seeing malvertising in their web browsres, etc. Security and access is always a balancing act you have to dance but it’s better to highly restrict then loosen those restrictions to allow more access in a managed way.
Clients we work with are far more secure at half the price and that’s a fact. Cisco isn’t value. The reason companies promote it is because they have a vested financial interest in doing so and don’t do so because it’s technically the strongest solution. VARs also rely on Cisco’s engineering (I use that term loosely…so loose I think I just lost a wheel) to help them when they can’t figure something out which actually shows their weakness as a VAR and not their strength. You’ll often hear things said like…I’ll have to open up a “TAC” with Cisco. TAC means “Technical Assistance Center” which means they’re calling Cisco for technical support further delaying resolution. The VARs like the company at the meeting I attended isn’t anyone I’d recommend doing business with unless they charged less. See that’s the key! VARs like that company get by on their marketing, the assistance from Cisco and the environments they’re in that aren’t too complicated. An entire industry has been built by MBA’s to put up this “professional services” illusion and an “engineering” veneer when reality can’t be further from the truth! They’re a commodity and should charge far less than their $145 dollars an hour, extra for “after regular business hours”, even more on a Saturday, even more on a Sunday and if it’s a Sunday and a holiday…yikes, you’re looking at $225 per hour! Express IT Solution can put that stuff in but we prefer not to and with good reason as I hope we’ve demonstrated. We’re always on, we don’t charge extra for nights, weekends or holidays either! How awesome is that?
Our blocking methods block what Talos should be blocking and far more. Our multi-layerd approach beyond the firewall protects your infrastructure from server to workstation to phone.
If you’re interested in knowing how you can protect your organization for less reach out and inquire. It might be the best thing you ever did for your organization even if it’s not a cyber security issue since we also develop software, IoT (Internet of Things) and have special skill sets that can do anything from web to databases! We are true IT solution providers.
800-864-9497
[si-contact-form form=’1′]